Introducing BeyondTrust.
The Modern Approach to Privilege Management
BeyondTrust is the most privileged access management solutions focus passwords. It is different with its Universal Benefits Management approach to cybersecurity which protects every user, asset and session throughout the campaign. Implemented as SaaS or on-premises, BeyondTrust’s Universal Benefits Management approach simplifies deployment, reduces costs, improves usability and minimizes privilege risks.
Enterprise Cloud Security
Protect your business with the most proven PAM solutions for the cloud.
Protect Every Privilege, Every Time
Trusted by more customers, our Universal Privilege Management approach creates a frictionless
experience for users, enabling the right level of access at just the right time.
The BeyondTrust Advantage
BeyondTrust serves more organizations than any other Privileged Access Management vendor. More than 20,000 customers, including 70% of the Fortune 500, trust us to improve cyber security and efficiency. We've helped more customers deploy in the cloud than anyone else. And customers rate our support organization with 96% satisfaction.
Promising Features of BeyondTrust:
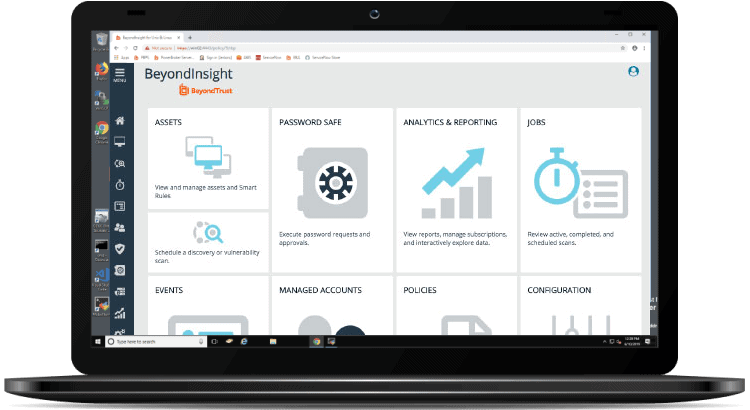
Go Beyond the Password™ with Universal Privilege Management Solutions
The BeyondTrust Privileged Access Management portfolio is an integrated solution that provides visibility and control over all privileged accounts and users. By uniting the broadest set of privileged security capabilities, the platform simplifies deployments, reduces costs, improves usability, and reduces privilege risks.
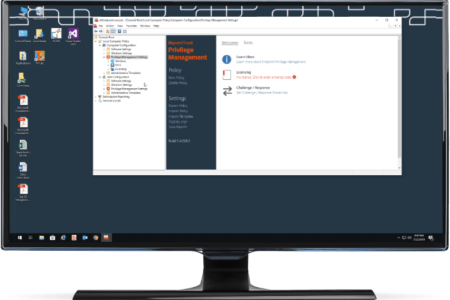
Endpoint Privilege Management
Stop malicious attacks, including malware and ransomware, by assigning just-in-time privileges and controlling applications on Windows, Mac, Unix, Linux, and networked devices - all without hindering end-user productivity. Plus, bridge the gap between Windows and other operating systems by extending Active Directory’s Kerberos authentication and single sign-on (SSO).
Privileged Password Management
Password Safe reduces the risk of privileged credential misuse through automated privileged password and session management. DevOps Secrets Safe secure and manage secrets used in DevOps environments. Achieve complete control and accountability over privileged accounts.
Testimonials
BeyondTrust testimonials have an aggregate content usefulness score of 4.7/5 based on 2016 user ratings.

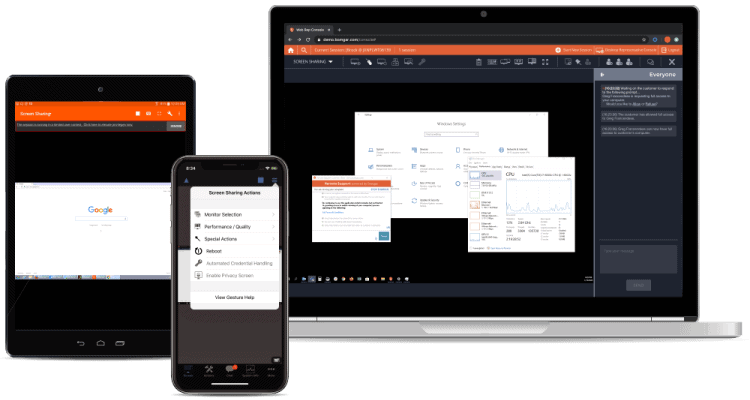
We take advantage of a number of Bomgar features to connect to and monitor the student’s computer. At the end of the day, what we accomplish with Bomgar distinguishes us from our competition. To make this an authentic, online proctored environment, we must dot all the i’s and cross all the t’s from the institution’s perspective. Bomgar makes that possible.
Tim Dewey
CHIEF OPERATING OFFICERFrequently Asked Questions
What is Beyond Trust ?
How do I install Beyond Trust?
Being the Swiss Partner of Beyond Trust, Kidan is responsible for aiding with professional services, such as installing, implementing, configuring, training, and supporting the company to ensure an effective on-boarding of Beyond Trust.
To make it even better, Kidan even provides advice on top of it all!
Get in touch with us to know more.
What is Privileged Access Management ?
What permissions do I need in order to be able to install and run Privileged Identity tools?
Is it possible to use an LDAP query to pare down the list of servers in my systems list in Privileged Identity tools?
Want to continue the conversation?
Thank you for your interest in BeyondTrust. Please fill out the form below to ask a question or request assistance.





